Today, mobile payments and digital solutions are rapidly becoming widespread. TR Karekod, Türkiye’s QR code payment system, stands out as one of the most important components of this digital transformation. Developed by the Interbank Card Center (BKM), TR Karekod provides a secure, fast, and user-friendly payment infrastructure.
TR Karekod continues to spread rapidly across many different sectors—especially retail, services, and e-commerce—by simplifying the user experience for both member merchants and cardholders at the same time. In this article, we will cover the technical infrastructure of the TR Karekod system, its use cases and benefits, the Airapi KYS product, and the KYS application process.
TR Karekod and the QR Code Routing System (KYS) are not structures that replace the existing card-based payment system; rather, they are positioned as a complementary layer that makes card payments mobile, contactless, and QR-based. Transactions are still carried out in the background between card-issuing and card-accepting institutions using the authorization and security infrastructure of card payment systems.
What is TR Karekod?
BKM TR Karekod is a payment method infrastructure developed and promoted by the Interbank Card Center (BKM). TR Karekod refers to a standard QR code infrastructure in Türkiye and enables payments to be made quickly, securely, and easily. It has been created in compliance with the regulations based on Law No. 6493 on Payment Services and Electronic Money Institutions of the Central Bank of the Republic of Türkiye. These regulations define the scope of payment transactions carried out using QR codes and regulate the procedures and principles regarding the generation and use of TR Karekod in payment services.

Figure 1: TR Karekod Example
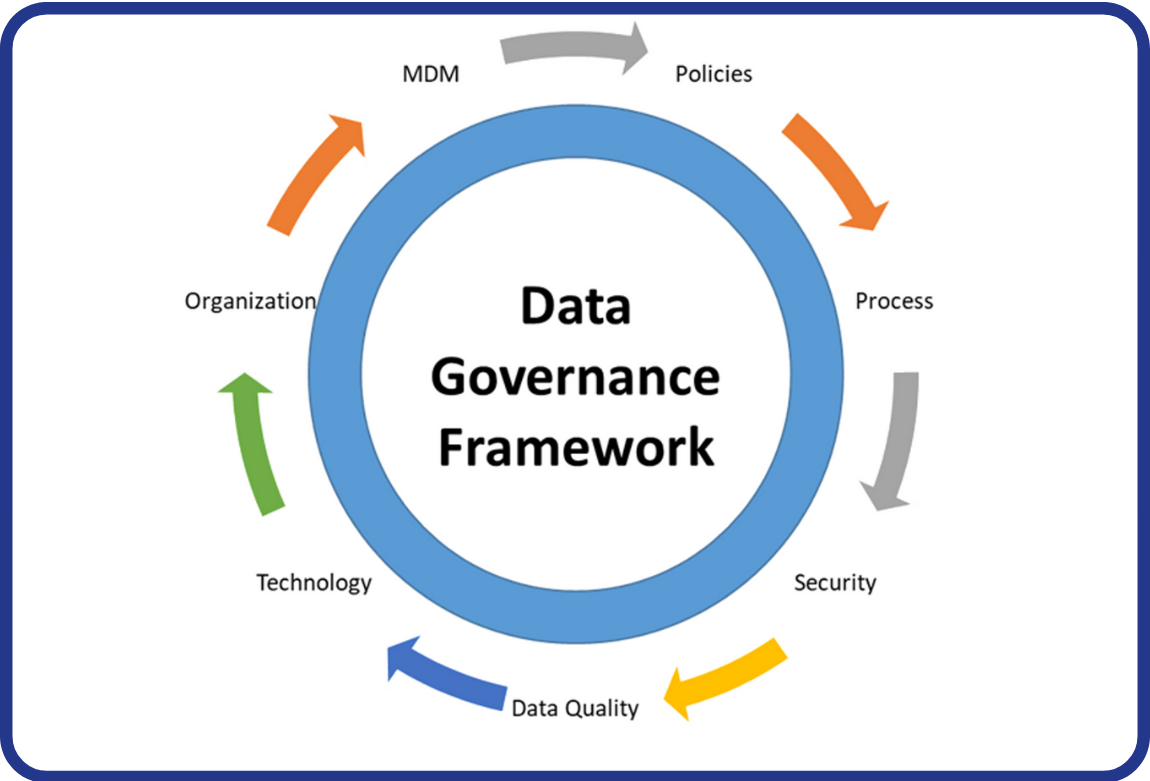
What is the QR Code Routing System (KYS)?
KYS: It is an infrastructure established and operated by BKM under the Regulation, enabling the transfer of QR codes and the information contained within them between payment service providers. In the KYS system, there are parties such as the Receiver, Sender, Card Issuer, and Card Acquirer.
Parties of the KYS System:
Receiver: Represents the real or legal person to whom the funds subject to the payment transaction are intended to be delivered.
Sender: Refers to the real or legal person who issues a payment order from their own payment account or without having a payment account.
Card Issuing Institution: Refers to institutions that establish a debit or credit card system and are authorized to issue cards under this system, as well as institutions authorized to issue cards that qualify as payment instruments under the Law.
Card Accepting Institution: Refers to institutions that establish a debit or credit card system and are authorized to make merchant agreements under this system, as well as institutions authorized to accept cards that qualify as payment instruments under the Law.
TR Karekod Usage Areas
TR Karekod technologies have a wide range of use cases such as EFTPOS (PCI-compliant standalone POS) terminals, ÖKC (cash registers integrated or connected with POS applications) devices, ATMs, and mobile payment applications, thereby simplifying the payment process across many platforms. Suitable for use in both physical and digital environments, this system provides speed and security for businesses and consumers.

Figure 2: Representative TR Karekod usage areas
Physical Stores
TR Karekod works integrated with POS devices to enable fast payments in stores. It is widely used in high-transaction locations such as supermarkets, restaurants, and clothing stores. Users can quickly complete payment transactions by scanning the QR code generated at the checkout with their mobile applications.
Online Shopping
TR Karekod can also be used on e-commerce platforms. By generating a QR code via a virtual POS, consumers can make secure payments for their online purchases. This structure eliminates the risk of directly entering credit card information and enables users to pay quickly and easily through mobile applications.
ATMs and Mobile Payment
The use of QR codes at ATMs is also becoming increasingly common. By scanning the ATM QR code via a mobile application, cardless cash withdrawal transactions can be performed. While this method enables users to withdraw money securely, it also helps prevent issues such as ATM fraud. In 2024, the cash deposit function via TR Karekod at ATMs was introduced by BKM, and banks are expected to become compliant with this process by the end of the first quarter of 2025.
Having summarized the usage areas of TR Karekod as above, it will also be useful to summarize the business usage models related to this section:
QR Code Usage Models
- Scanning the QR Code Generated by POS/ATM via the Card Issuer’s Mobile Application
In this model, the POS terminal or ATM generates a QR code, and the transaction is completed via the card issuer’s mobile application. Two types of QR codes can be used: BKM Long QR Code Format (UKF) and BKM Short QR Code Format (KKF).
a. Payment Flow Initiated by Generating a BKM Long QR Code Format from POS
The transaction amount is determined at the terminal and a QR code compliant with the BKM UKF structure is generated.
The cardholder scans the QR code generated at the terminal via their mobile application.
The cardholder selects the card to be used via the mobile application. Card information is transmitted in encrypted form to the Card Issuer via KYS (QR Code Routing System).
The Card Acquirer completes the authorization process and sends an approval or rejection response to the mobile application that initiated the QR code.
The transaction is completed on the POS terminal.
b. Payment Flow Initiated by Generating a BKM Short QR Code Format from POS
The transaction amount is determined at the terminal and a short QR code is generated.
The cardholder scans the QR code and the short QR code value is transmitted to KYS.
After the cardholder approves the transaction, the data is routed to the Card Acquirer via KYS.
After authorization is completed, the transaction is finalized at the terminal.
c. Cancellation/Refund Flow Initiated by Generating a QR Code from POS
When a cancellation or refund transaction is initiated, the sale transaction is queried and a cancellation/refund QR code is generated.
The cardholder scans the QR code with their mobile application and approves the transaction.
Card information and transaction details are encrypted and routed to the Card Acquirer via KYS, and the transaction is completed.
d. ATM QR Code Transaction Flow
While on the ATM main screen, the cardholder scans the QR code with their mobile application and selects the card.
Card information is encrypted via KYS and transmitted to the Card Acquirer.
The ATM displays commission information for the transaction, and after approval, the transaction is completed.
- Scanning the QR Code Generated by POS via a Third-Party Mobile Application
In this model, the cardholder completes the payment using a third-party mobile application rather than the card issuer’s application. QR codes are also generated here in long and short formats.
a. Payment Flow Initiated by Generating a BKM Long QR Code Format from POS
The transaction amount is determined at the terminal and a long QR code is generated.
The cardholder scans the QR code via the third-party mobile application and selects the card.
Card information is encrypted and transmitted to the Card Issuer via MHSK (Mobile Service Server) and KYS.
Authorization is completed and the transaction is finalized on the POS terminal.
b. Payment Flow Initiated by Generating a BKM Short QR Code Format from POS
The transaction amount is determined at the terminal and a short QR code is generated.
The cardholder scans the QR code via the third-party mobile application. The application shares transaction details with KYS via MHSK.
After card information is verified and authorization is completed, the transaction is finalized.
c. Cancellation/Refund Flow
The cancellation/refund transaction is initiated, the transaction is queried, and a cancellation/refund QR code is generated.
The cardholder scans the QR code with their mobile application and approves the transaction. Card and transaction details are encrypted and transmitted via KYS.
The transaction is completed.
d. Notification of Authorization Result to the Mobile Application
The authorization result is transferred from the Card Issuer to MHSK via KYS.
MHSK forwards the received response to the mobile application.
The mobile application can display the authorization result to the user.
Technical Structure of TR Karekod
TR Karekod is more secure and faster than traditional payment methods. While transaction security is ensured through data encryption methods, users can easily make payments by scanning the QR code with their mobile devices. In addition, with static and dynamic QR code options, it supports multiple usage scenarios.
What Are Static and Dynamic QR Codes?
TR Karekod can be used in two different structures: static QR code and dynamic QR code.
Static QR code is a structure in which the same QR code is used for multiple payment transactions. It is especially preferred by small businesses and in situations requiring fast payments. The transaction amount and other information are fixed in the QR code.
Dynamic QR code, on the other hand, generates a different QR code for each transaction. This structure is used for large transactions or situations requiring higher security. The dynamic QR code contains customized data per transaction.
Technical Structure of TR Karekod
TR Karekod has a data structure compliant with international standards. The QR codes used during payment contain transaction information, payment amount, and security data. Transactions are carried out using two main QR code formats: BKM Long QR Code Format (BKM UKF) and BKM Short QR Code Format (BKM KKF).
BKM Long QR Code Format (UKF)
BKM UKF is a format that contains more information and is generally used as a dynamic QR code. This format includes merchant information, transaction amount, card information used in the payment process, and security data. For example, when shopping at a store, the QR code generated by the terminal is scanned via the customer’s mobile application and the payment is completed in this way.
The structure of the Long QR Code Format (UKF) is as follows:
- Merchant information and account details
- Transaction type (such as sale, cancellation, refund)
- Payment amount and currency
- Card information and authentication methods (such as PIN entry)
BKM Short QR Code Format (KKF)
BKM KKF is used for simpler transactions. Preferred in static QR code format, this structure contains less detailed transaction data and is generally used by small businesses for fast payment processes.
The structure of the Short QR Code Format (KKF) is as follows:
- QR Code Format Indicator
- QR Code Generator Code
- CRC Integrity Check
- Hash
- QR Code reference number
An example plain text value generated in the BKM short QR code structure could be as follows: 9908001234567890120123456789012345678901234567891280BE
The QR code image generated for this plain text would look like Figure 3.

Figure 3: Sample BKM short QR code image
QR Code Routing System with AirApi

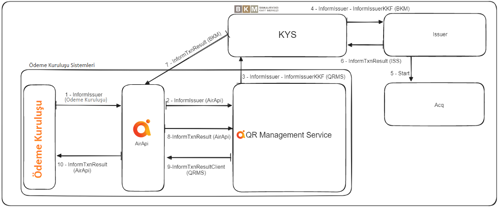
Figure 4: Airapi logo and KYS
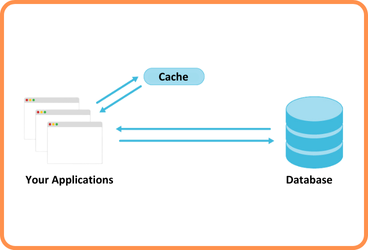
The Airapi KYS system has been developed using REST API architecture for communication between banks and payment institutions over BKM, and JSON data format for request/response message contents. Within this scope, the KYS system infrastructure has been made available to business partners as a new business module within Architecht’s Open Banking solution, the Airapi product. After the KYS infrastructure was added as a new business module to the Airapi product, it successfully passed all certification tests determined by BKM.
The main responsibilities of Airapi KYS can be listed as follows:
- Transferring QR code data between payment service providers.
- Ensuring secure transmission of encrypted data.
- Verifying transaction accuracy and ensuring data integrity.
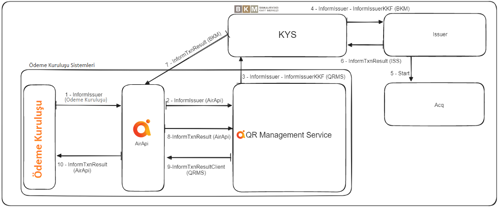
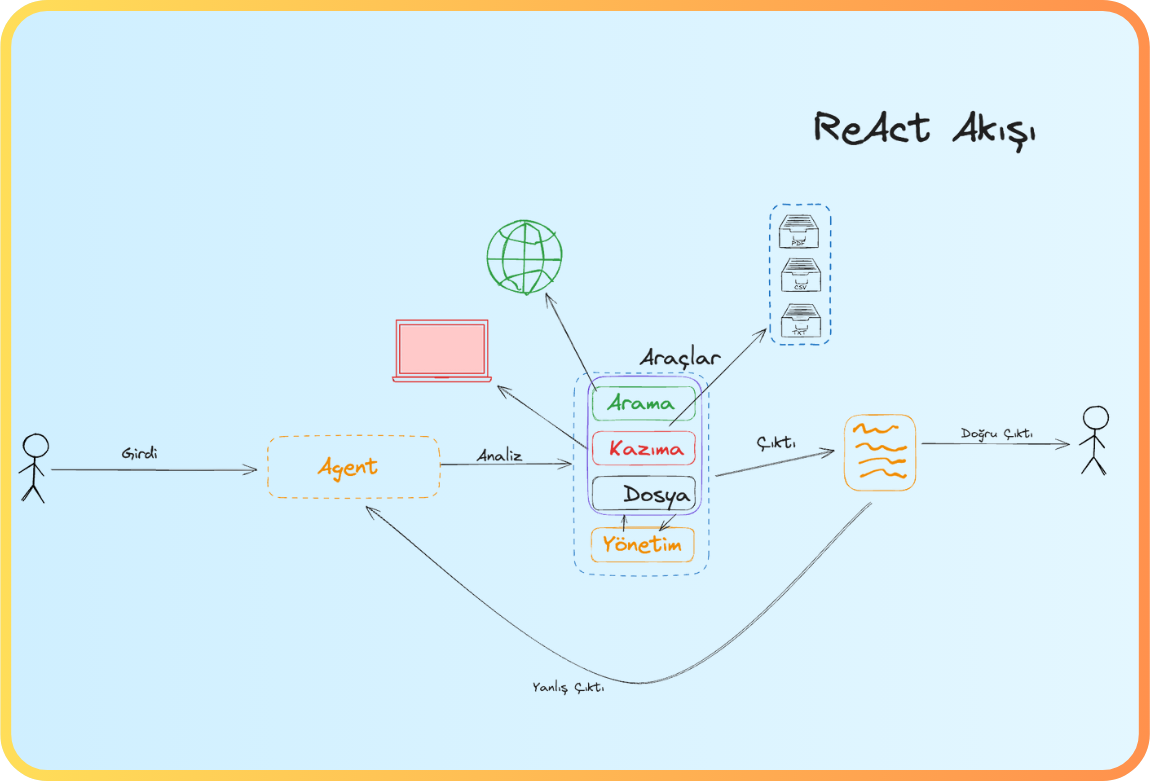
Figure 5: Sample flow: Making payments with QR codes via Third-Party (Payment Institution) Wallet Applications
The transaction steps of Payment Institution wallet applications can be summarized as follows:
- A QR code is generated by the Card Accepting Institution.
- The user scans the generated QR code via their mobile application and selects the card for payment.
- Card information and transaction details are transmitted to the Card Issuer via KYS.
- The Card Issuer verifies the authorization data and approves the transaction.
- As a result of the transaction, information that the QR code transaction has been completed is transmitted to the mobile application via KYS.
KYS uses AES encryption and hash algorithms together to ensure data security during transactions. In this way, data integrity is preserved and securely transmitted while being transferred from one payment provider to another. Within the Airapi KYS System, service infrastructures such as QR Code Generation Service, QR Code Reading-Validation Service, Issuer Notification Service, Transaction Result Notification Service are provided, enabling payment institutions to integrate quickly with the KYS system.
KYS Security Layers
TR Karekod uses a series of advanced security layers to ensure that payment transactions are carried out securely. Especially in digital payment systems, preventing fraud and abuse is of critical importance. TR Karekod has developed its security layers in accordance with international standards, thereby ensuring that transactions are completed securely. These layers include:
1. AES Encryption (Advanced Encryption Standard)
The foundation of TR Karekod’s security infrastructure is AES (Advanced Encryption Standard) encryption technology. AES uses a symmetric encryption algorithm to ensure data security. Symmetric encryption is a method where the same key is used for both encrypting and decrypting data. AES can operate with 128-bit, 192-bit, and 256-bit key lengths. TR Karekod generally uses 256-bit AES encryption to provide the highest level of security.
AES Encryption Process:
Encryption Key: The data used during payment is encrypted with an AES encryption key generated by the card issuing institution. This key ensures secure transmission of transaction data.
Data Encryption: Transaction data contained in TR Karekod (such as card number and transaction amount) is encrypted using the AES algorithm. This ensures that the data can only be decrypted by the relevant parties.
Data Decryption: The payment provider decrypts the encrypted data using the same encryption key and verifies the transaction.
Strength of AES:
The symmetric structure of AES and its 256-bit key length provide security that is nearly impossible to break. Considering the current capacity of computer systems, this encryption technology is known to be resistant to brute force attacks. AES also provides high security without negatively affecting transaction times, as it is a fast encryption algorithm.
2. Hash Functions and Digest Security (Hashing)
Hashing is another important technique used in the security infrastructure of TR Karekod. Hash functions convert data into a fixed-length value. This process is used to verify data integrity. TR Karekod uses hash values to ensure the integrity of payment data and to prevent the use of fraudulent QR codes.
How Does the Hash Process Work?
A data set (for example, transaction amount, merchant information, card number) is subjected to a hash function, producing a fixed-length hash value.
The hash value is stored within the QR code during the transaction and transmitted to the payment provider along with the data.
The payment provider generates its own hash value using the same hash function and compares it with the hash value in the QR code.
If the two hash values match, data integrity is preserved. If they do not match, it indicates that the data has been altered and the transaction is canceled.
Hash functions do not perform encryption; instead, they verify whether data has been transmitted without being corrupted or tampered with. In TR Karekod, strong hash algorithms such as SHA-256 are used. SHA-256 generates 256-bit hash values, providing high security.
3. PIN Verification and PCI Compliance
In payment transactions, a PIN verification mechanism is used to authenticate the user and ensure that the transaction is carried out by the authorized person. TR Karekod supports PIN verification processes on PCI DSS (Payment Card Industry Data Security Standard) compliant systems. PCI DSS is a standard created for data security in card payment systems and includes all necessary security measures to protect card information.
PIN Verification Process:
When making a payment with a QR code, the user enters their PIN information via the mobile application before approving the transaction.
The PIN information is verified by the payment terminal or mobile device, and the transaction is completed after PIN verification.
PIN verification is used to increase the level of security, especially for high-value transactions.
PCI Compliance:
TR Karekod works in compliance with PCI DSS-certified terminals, protecting card information and PIN data used in transactions. Devices with this certification meet specific security criteria in terms of data protection. For example, devices used during PIN entry (POS terminals or mobile devices) have security layers that prevent PIN data from being captured by unauthorized persons.
4. Data Privacy and Authorization
The TR Karekod system operates on the principle of minimum data sharing in every transaction. This means that no additional information is shared beyond what is necessary to complete the transaction. This approach ensures the protection of personal data and prioritizes privacy in transactions.
Data authorization mechanisms ensure that only authorized parties can access data during a transaction. For example, critical information such as card number or transaction amount is transmitted in encrypted form so that only the relevant payment provider can access it. Unauthorized persons or third parties are prevented from accessing this data.
With the security layers it provides, TR Karekod ensures a high level of security in payment transactions. Security mechanisms such as AES encryption, hash functions, PIN verification, and KYS offer a secure payment infrastructure for both users and merchants. This system not only provides speed and ease of use, but also creates a secure environment in terms of data security and transaction integrity.
QR Code Application Process
Information and documents regarding applications to BKM for obtaining a QR Code Generator Code or for participation in KYS are provided below.
Members that will obtain a QR Code Generator Code;
1. Karekod Üretici Kodu Başvuru ve Bildirim Formu must be completed and submitted to BKM,
Members that will obtain a QR Code Generator Code and also receive services from KYS;
1. Karekod Üretici Kodu Başvuru ve Bildirim Formu must be completed and submitted to BKM,
2. KYS Katılımcı Taahhütnamesi must be signed,
3. KYS Sorumlu Çalışan Bilgi Formu must be completed and submitted to BKM,
4. Members in the production environment must fulfill the administrative requirements specified under the “Participation in KYS” section of the QR Code Routing System Rules document,
5. Members in certification who have declared their participation must fulfill both the administrative and technical requirements specified under the “Participation in KYS” section of the QR Code Routing System Rules document.
References


 Back
Back